Prolaborate and Azure AD SAML Integration
Prerequisites
Your Prolaborate site should have a valid SSL Certificate.
If you don’t have an SSL Certificate, you can create a self-signed certificate yourself. Please get in touch with the Prolaborate team to know more about it.
Service Provider Configuration
To configure the Service Provider, click on Menu > SAML Single Sign On
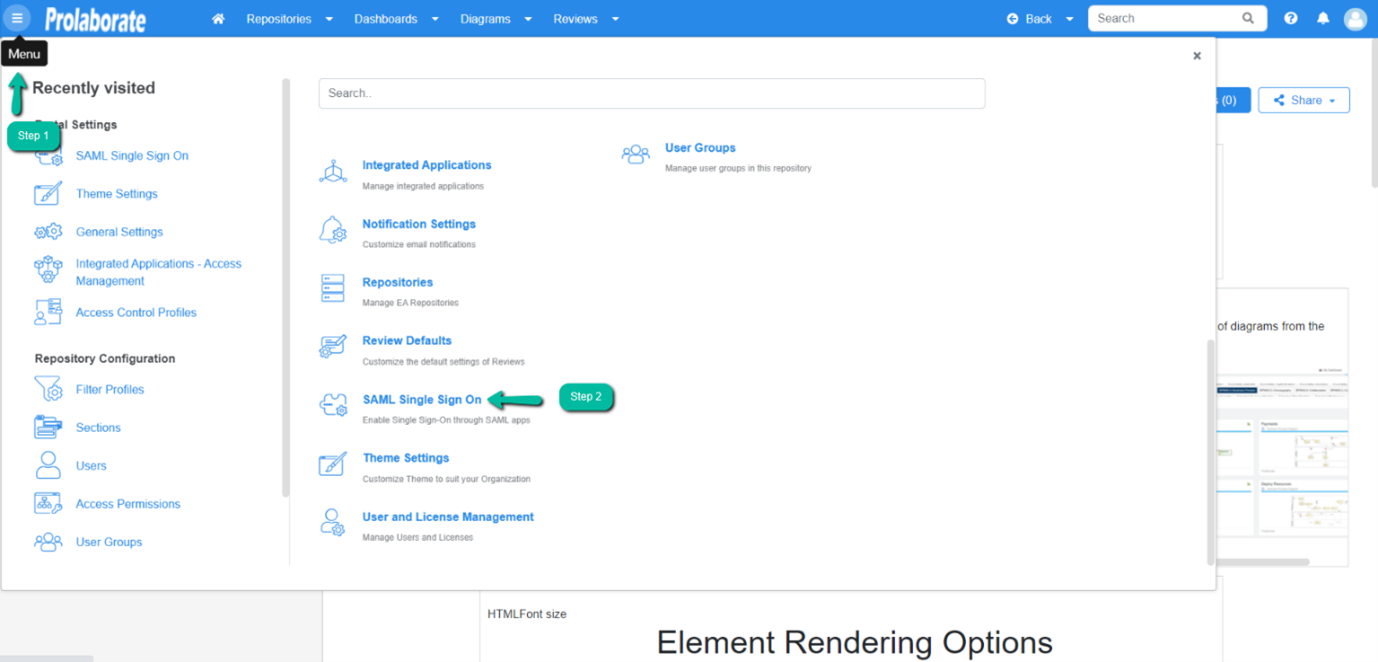
From the top of the page that opens, click on Enable SSO
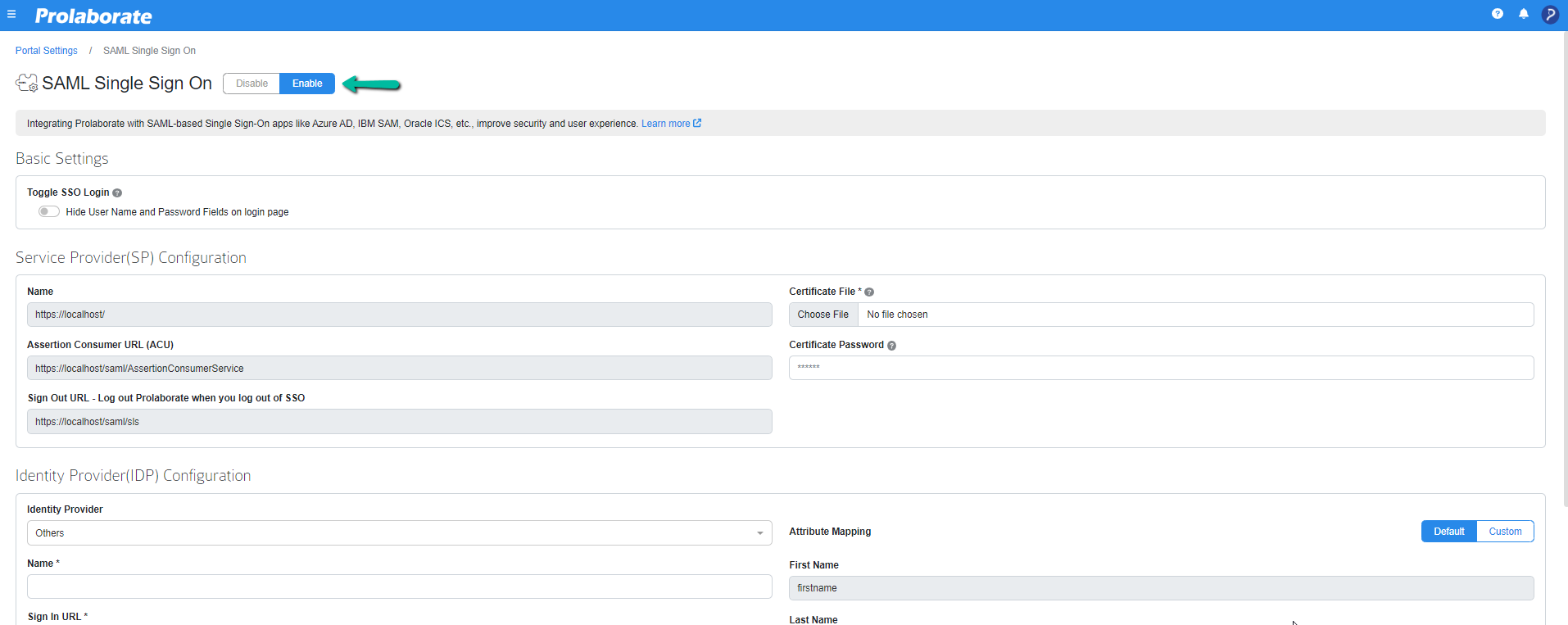
Under Service Provider Configuration
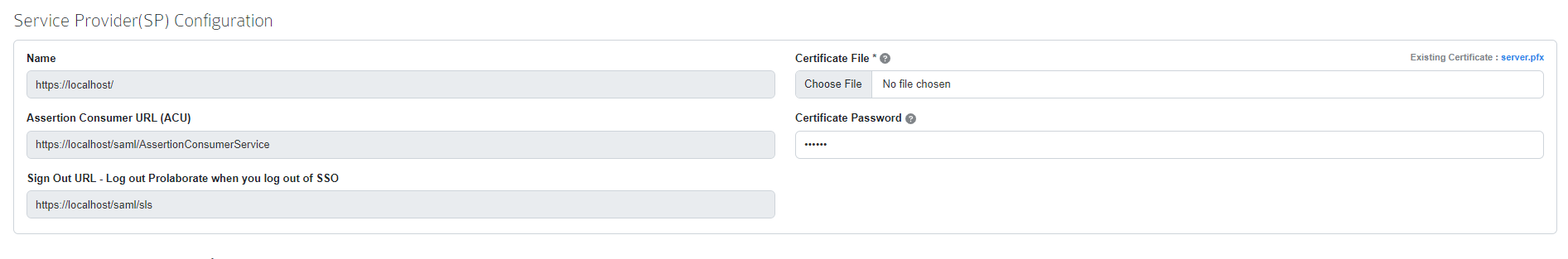
| Name | The name will be prefilled |
| Assertion Consumer URL | Assertion Consumer URL will be Prefilled |
| Certificate File | Choose the .pfx file of your SSL certificate |
| Certificate Password | Enter the Password of the .pfx file |
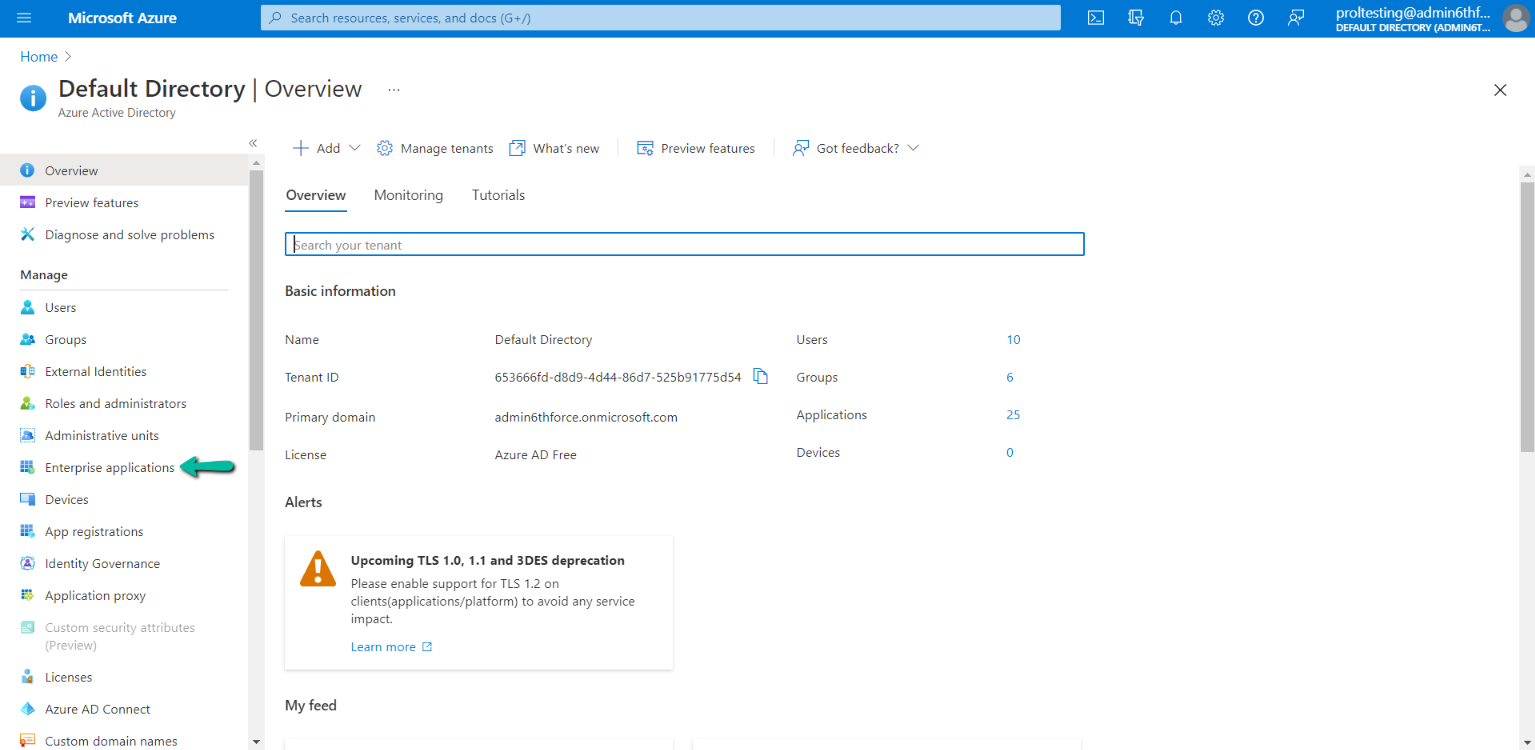
Configuring Prolaborate in Azure Active Directory
The following sections will elaborate on the steps involved in setting up Prolaborate in Active Directory (AD).
Create a new SAML Application
To create a SAML application, follow the below steps:
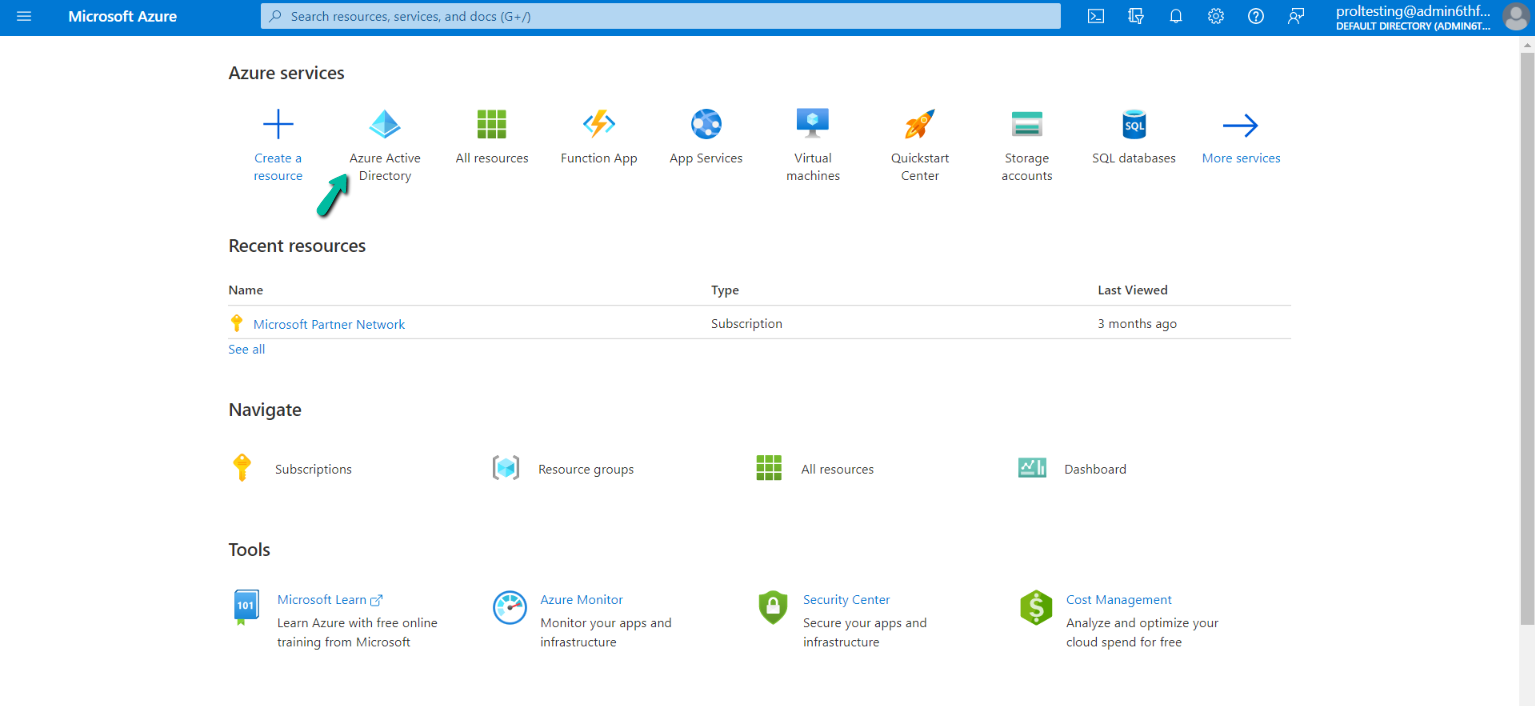
- Sign in to the Azure portal using your administrator account
- Click on Browse to the Azure Active Directory on the landing page
3. On the landing page click on Enterprise Applications.
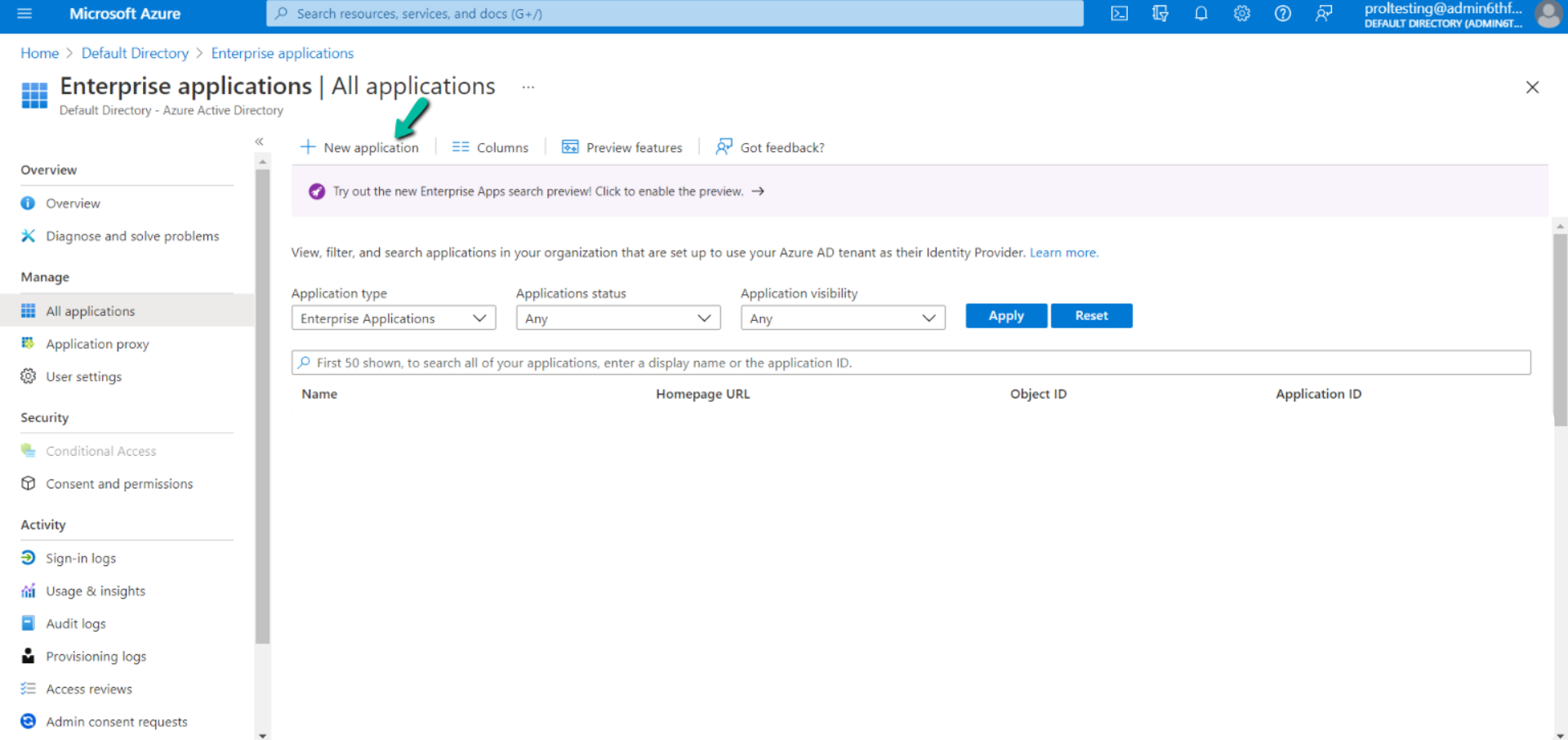
4. Now click on New Application
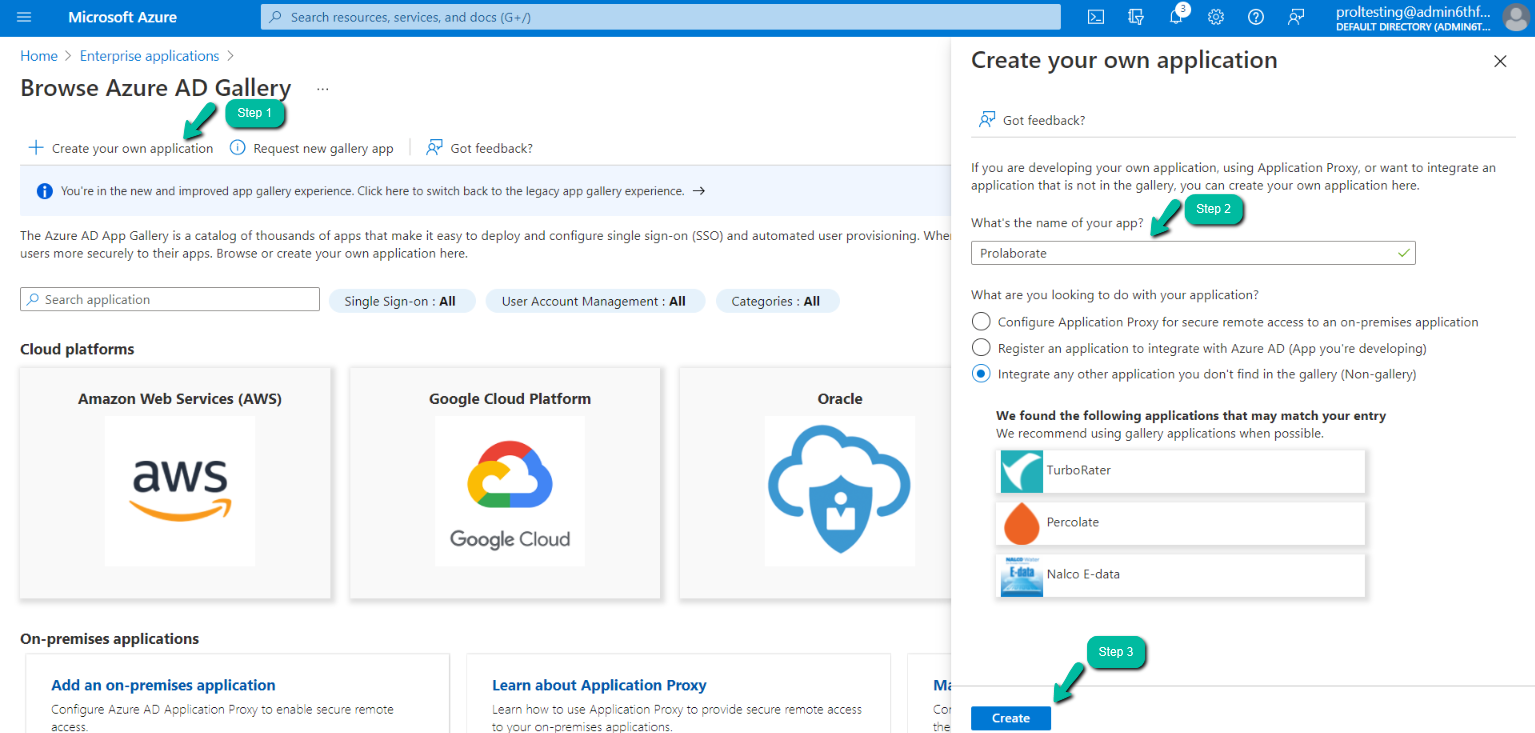
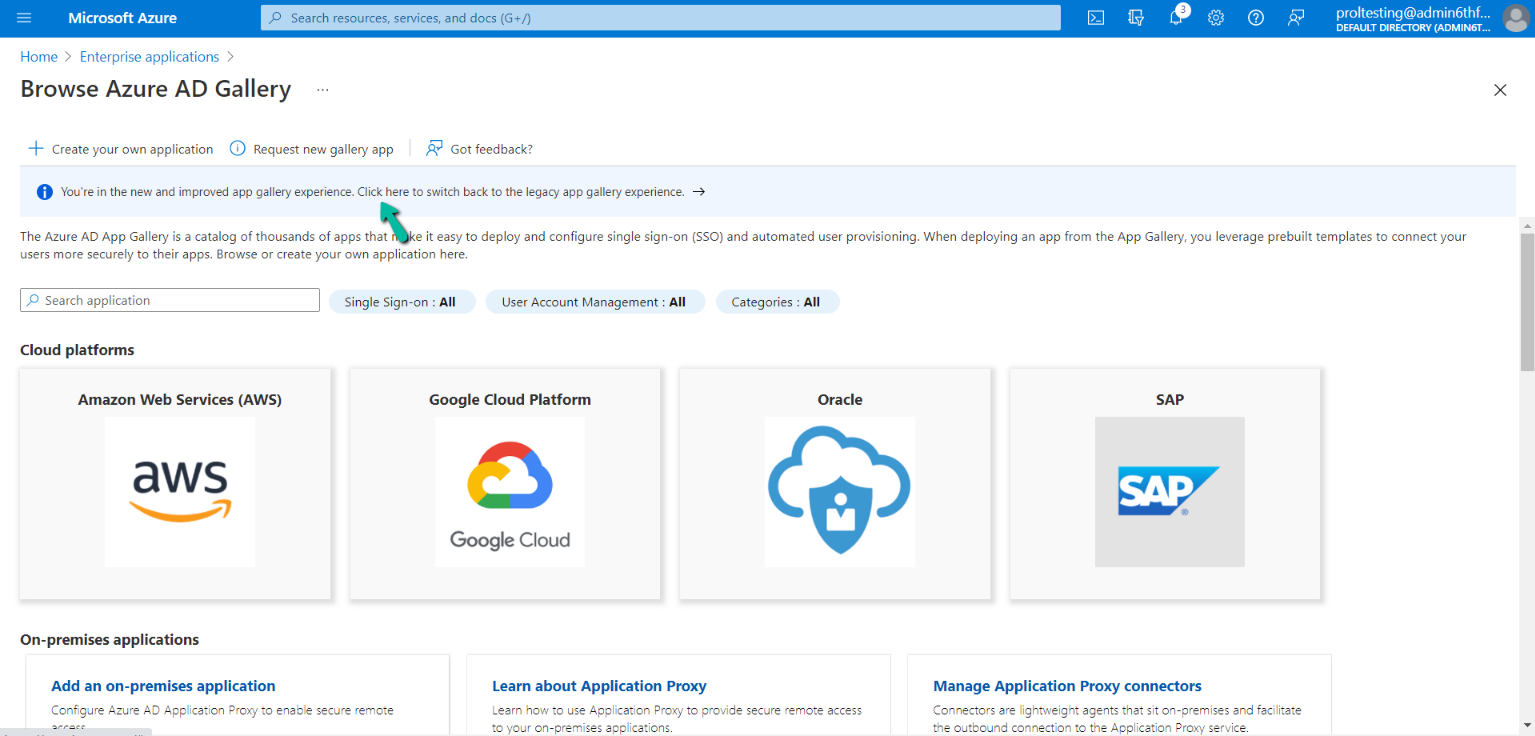
5. You will land In the Browse Azure AD Gallery, now click on Create your own application.
Note:
- Users can either use new app gallery or legacy app gallery to create an application
Create Application using New App Gallery (Recommended approach)
On the Create your own application form, enter the name of the app (i.e Prolaborate)
Make sure the default radio button option “Integrate any other application you don’t find in the gallery (Non-gallery)” is selected and click on Create
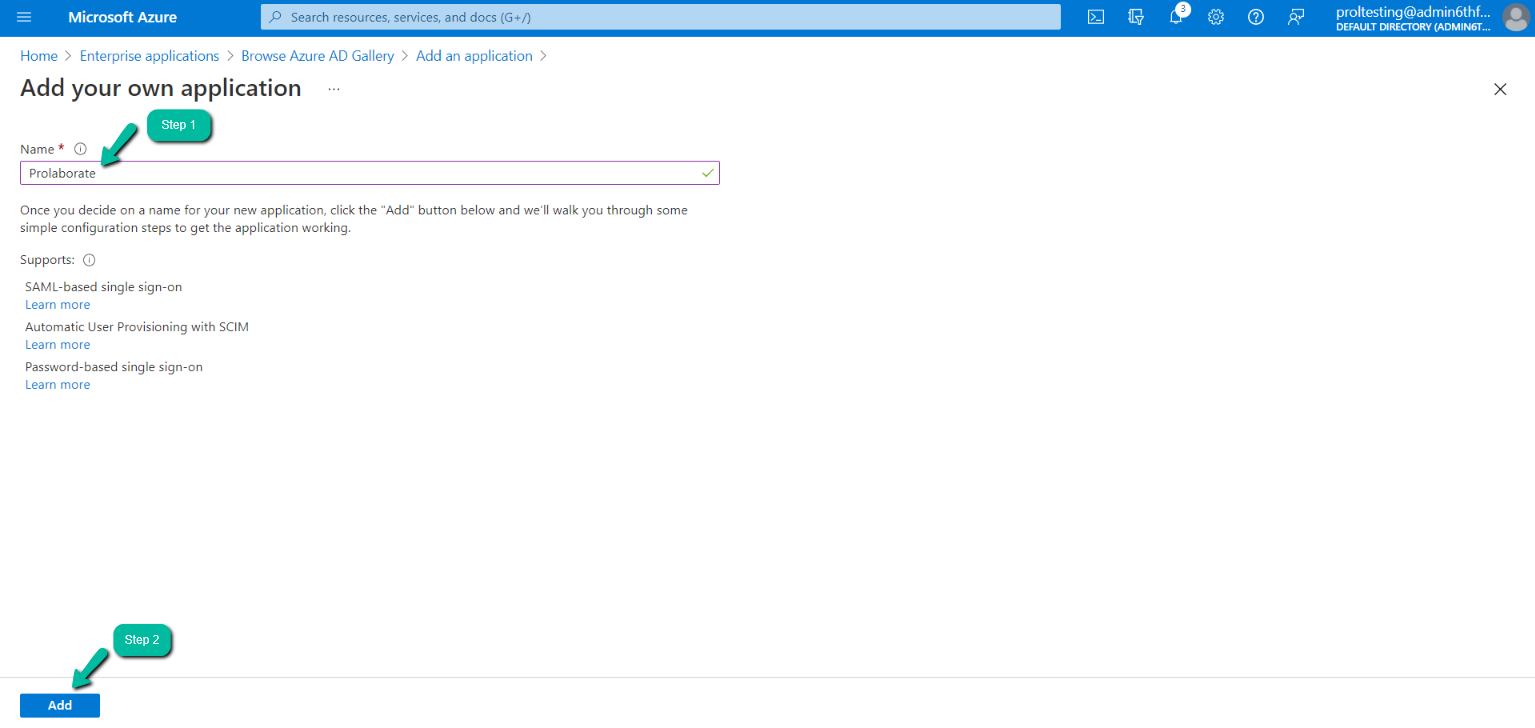
Create Application using Legacy App Gallery (Alternate to above approach)
Click on Click here to switch back to the legacy app gallery experience.
On the Add an application page, choose the Non-gallery application.
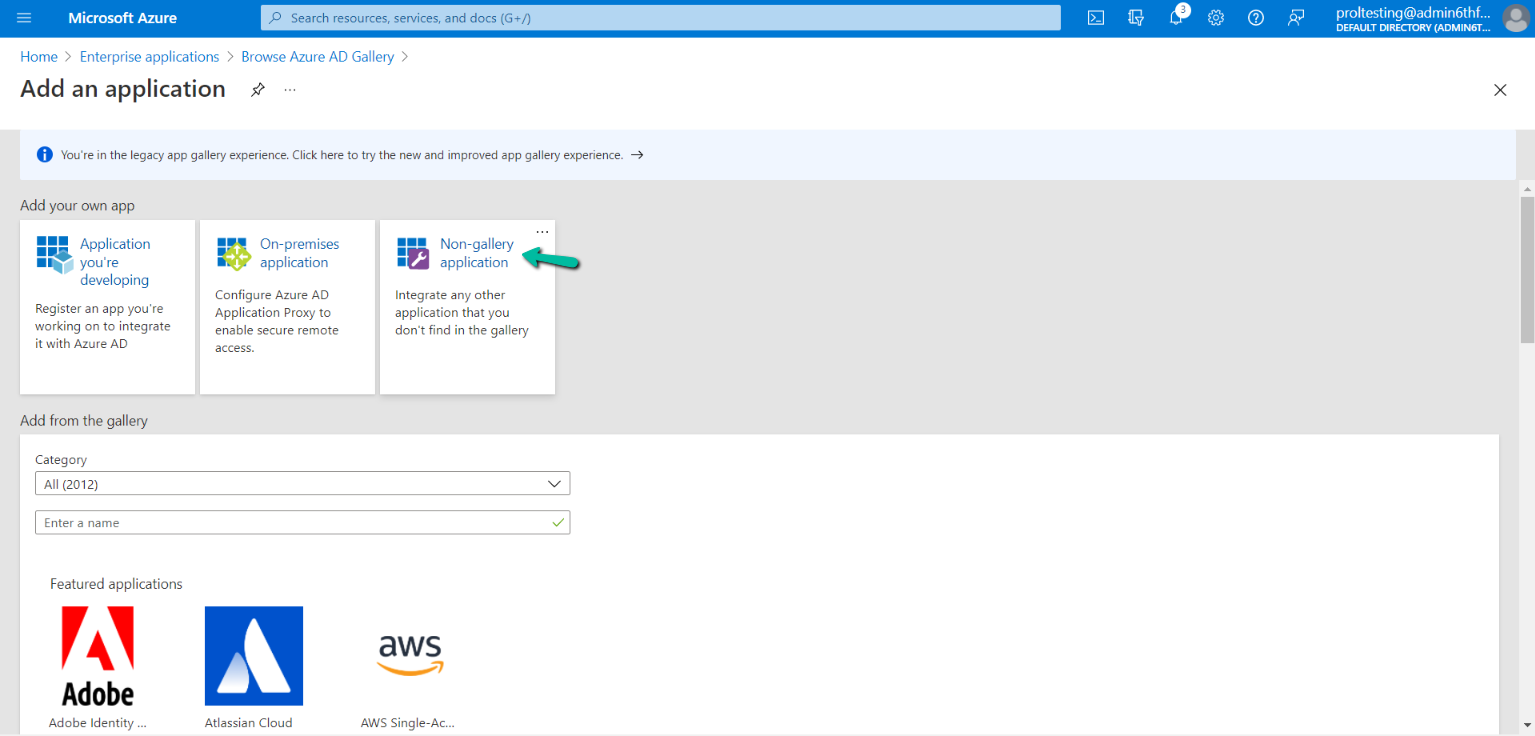
Now you will land on the Add your own application page. Enter the name of the app and then click Add
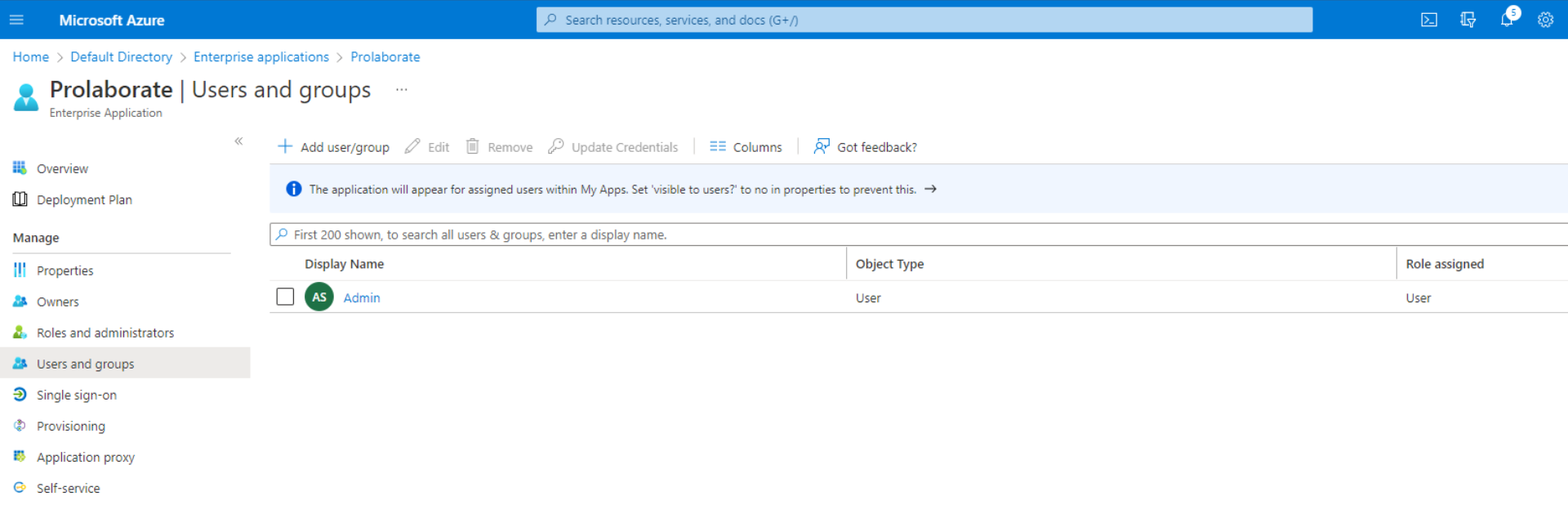
Assign Users
In this section, we will specify which AD users can access Prolaborate.
Once your application is created you will land on the Overview page and then select Assign users and groups
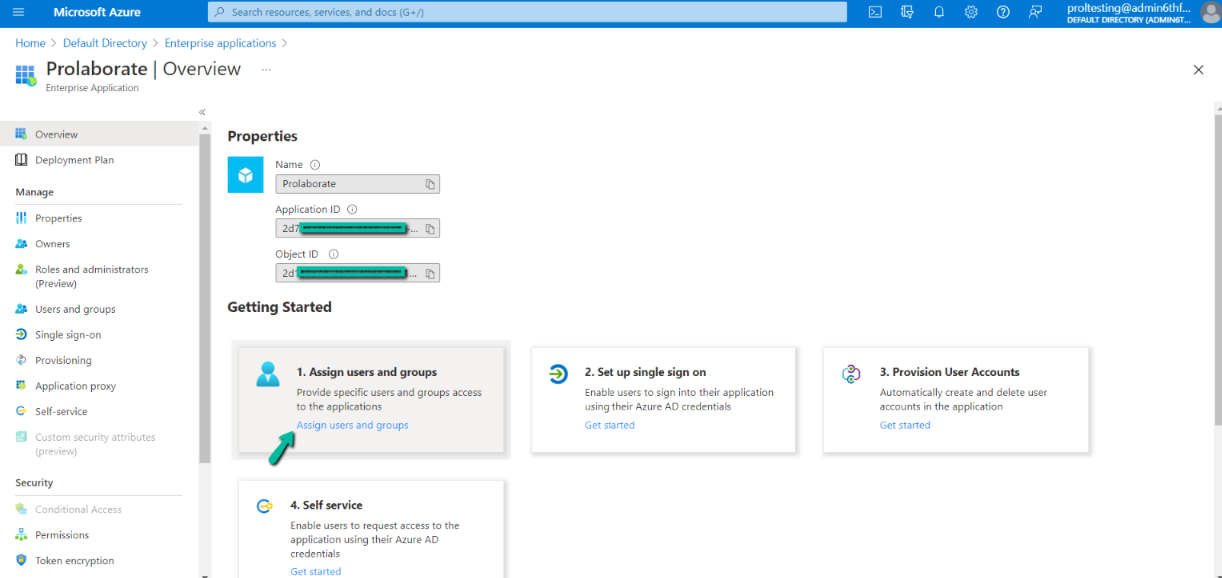
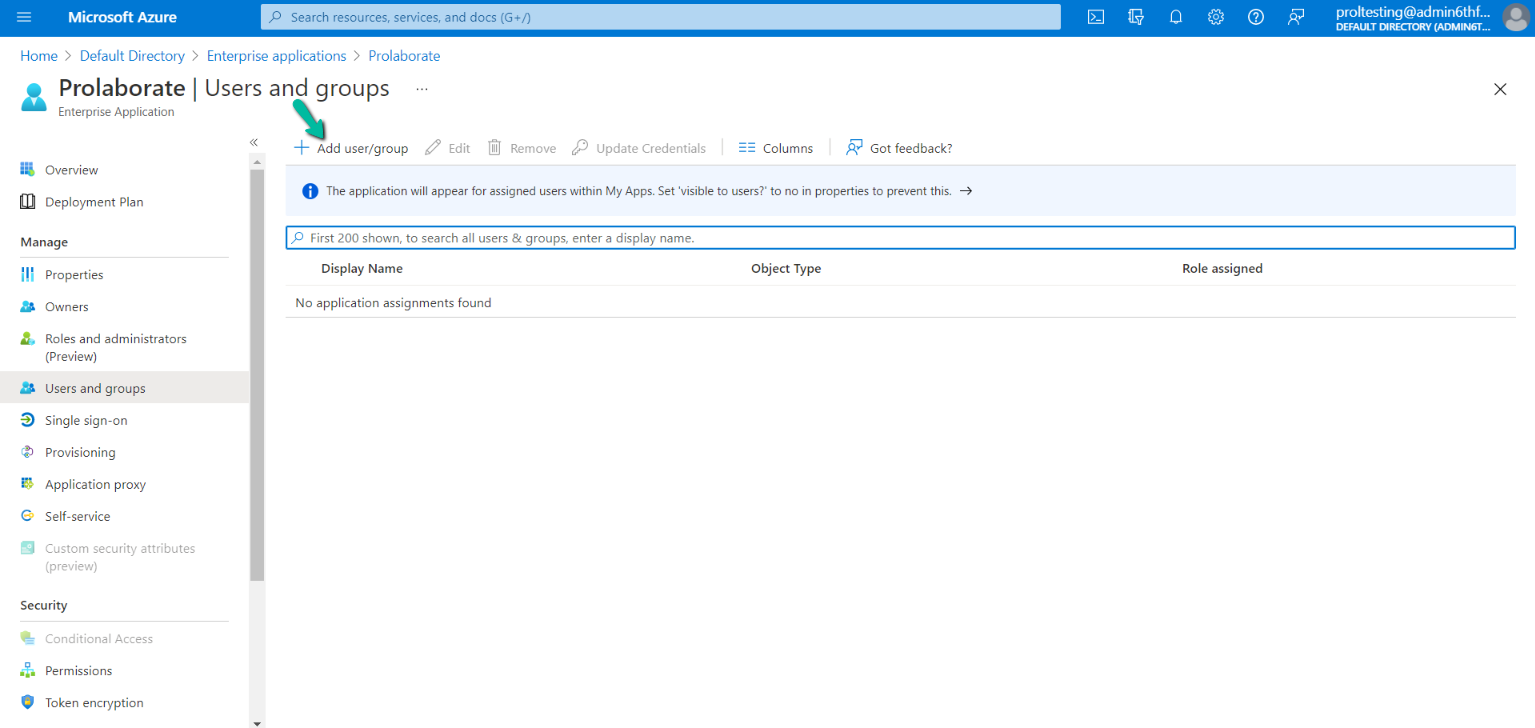
You will land on the users and groups page and now click on Add user/group
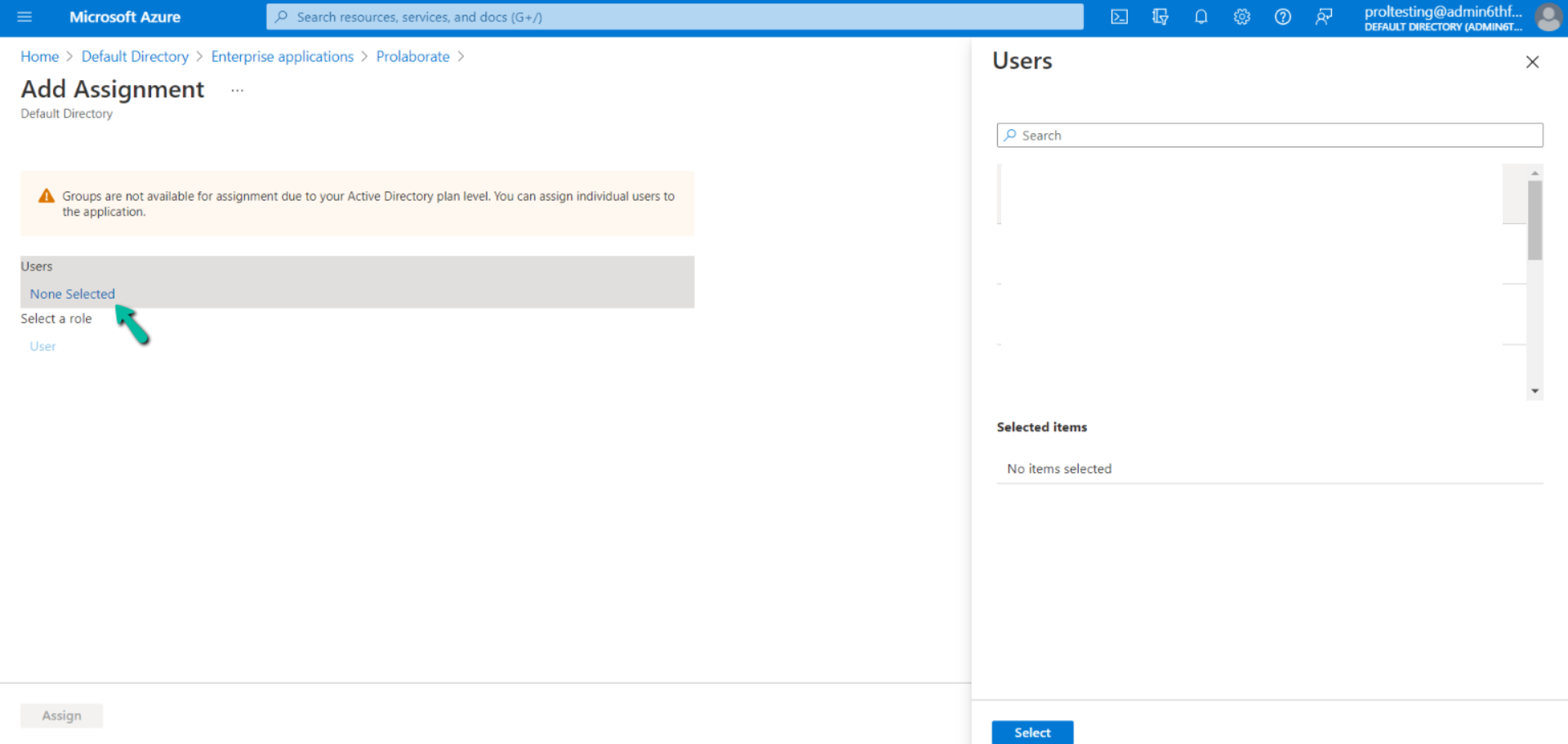
On the Add Assignment page by default no user will be selected to add users to the application click on None Selected under Users.
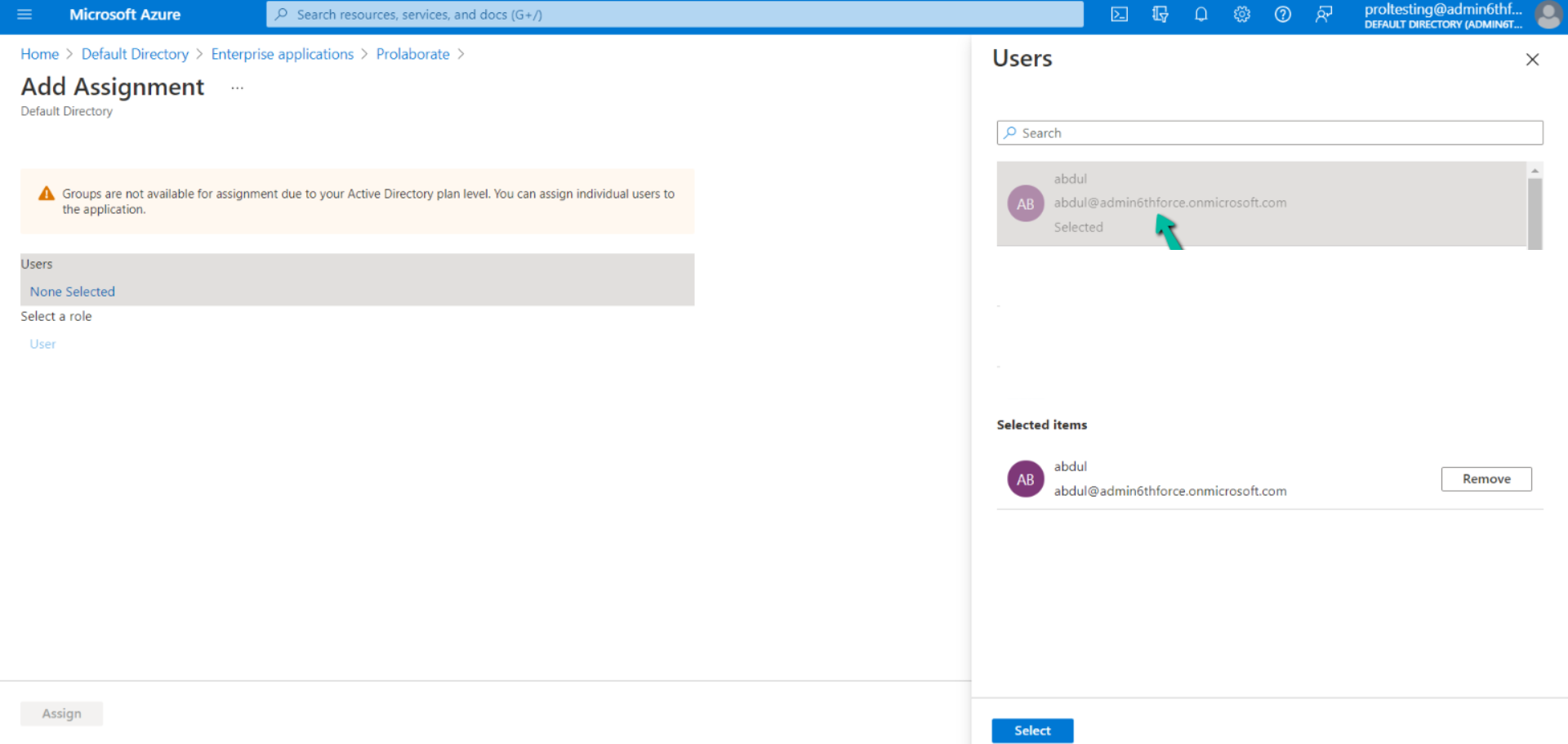
Now click on the users from the list who do you want to add as users and click on Select
Now click on the Assign
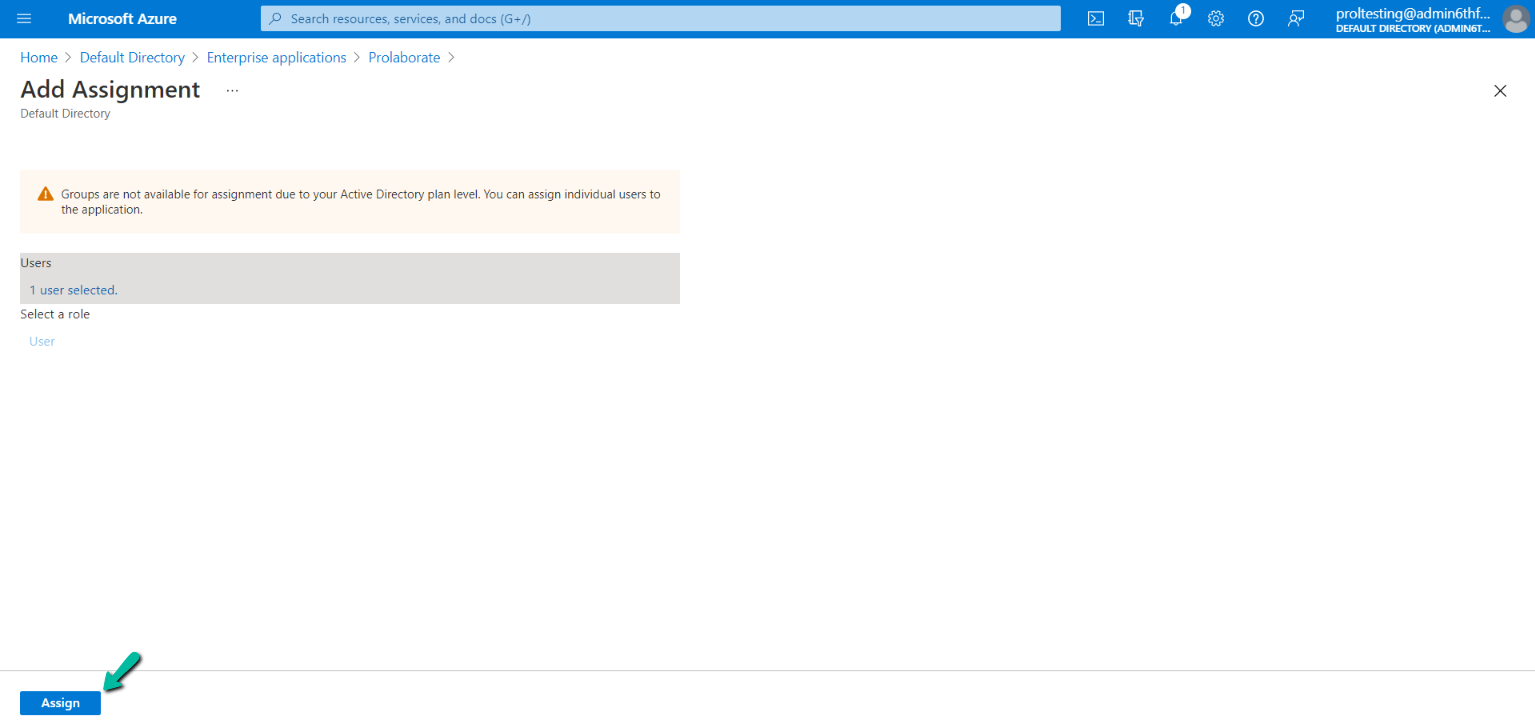
The users whom we have selected will now show up on the Users and groups page.
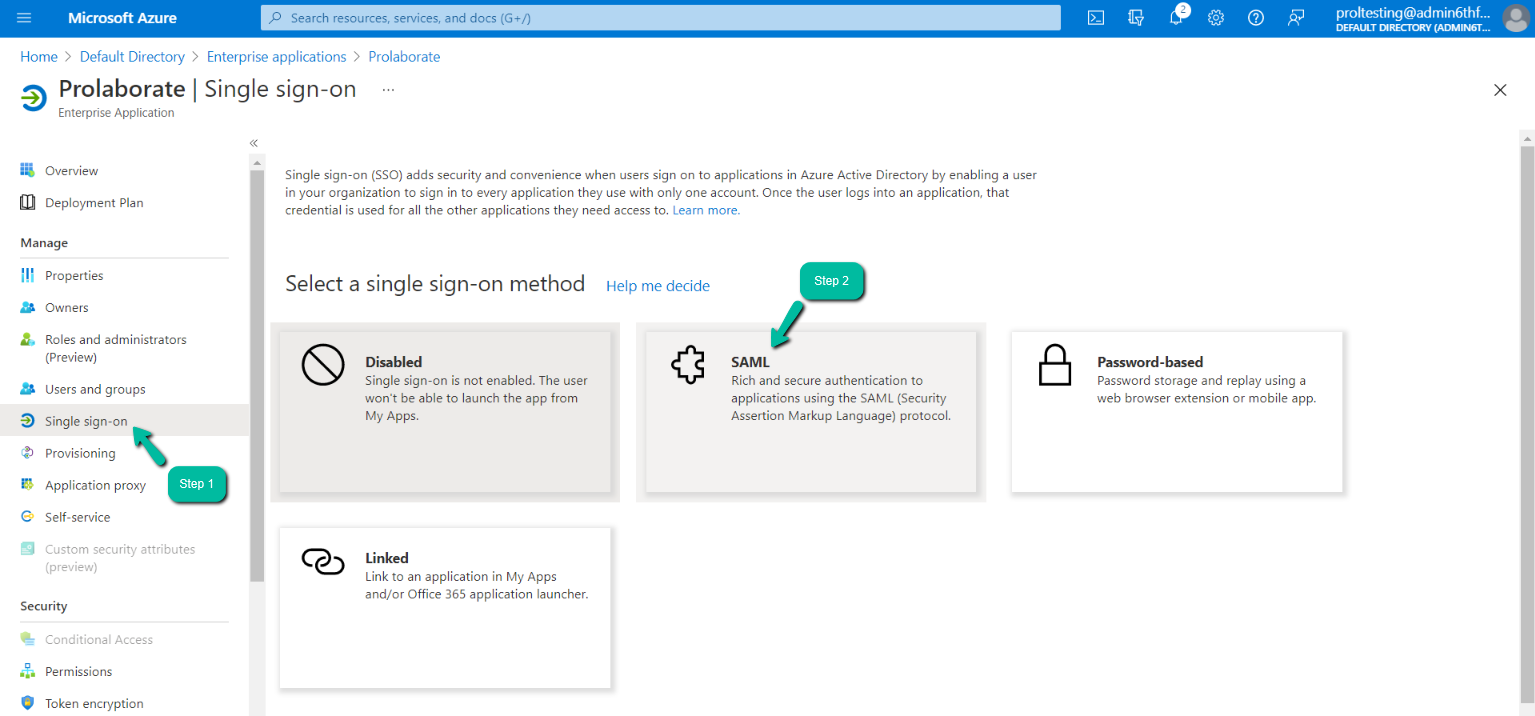
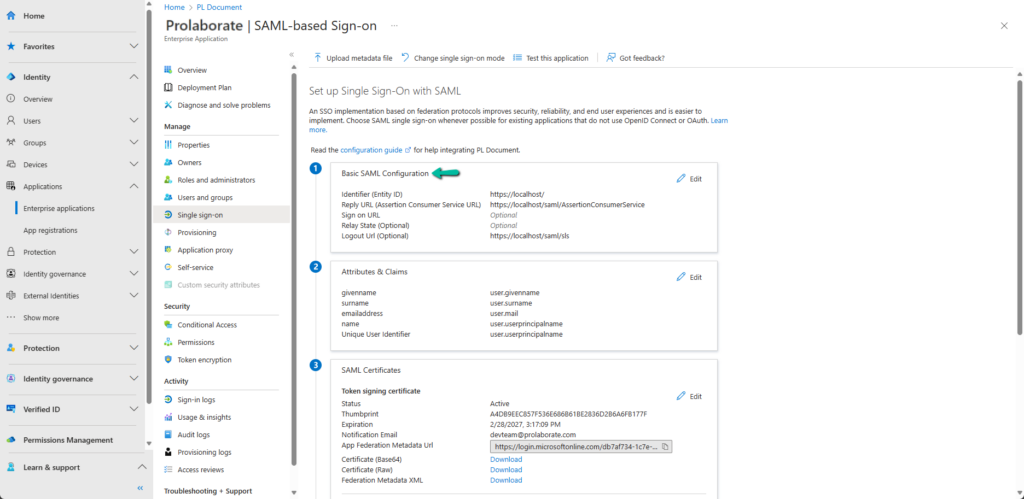
SAML Single sign-on Configuration
Follow these steps to configure SAML Single sign-on and get the required information that is needed to configure from the Prolaborate part:
Click the Single sign-on option and select SAML
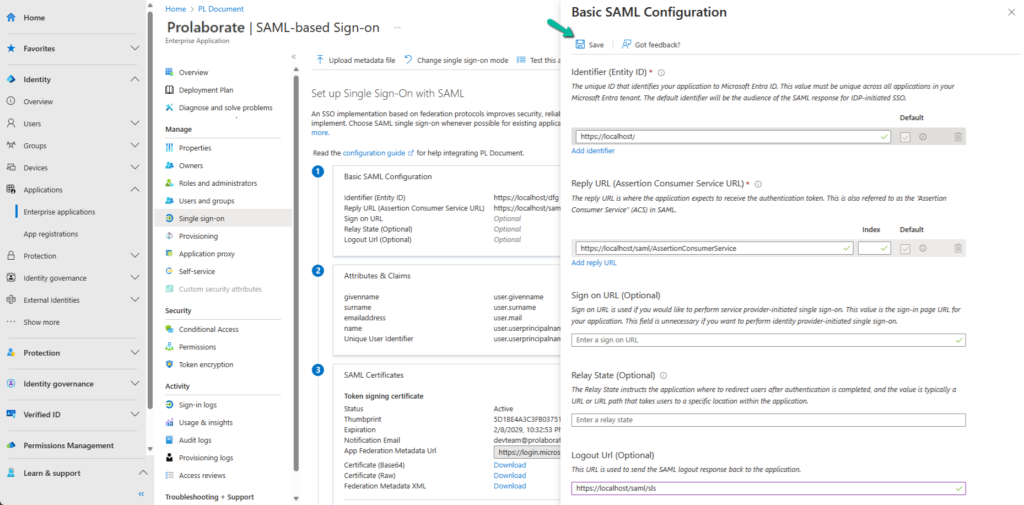
On the Set up Single Sign-On with SAML page click on the Edit icon under the Basic SAML Configuration
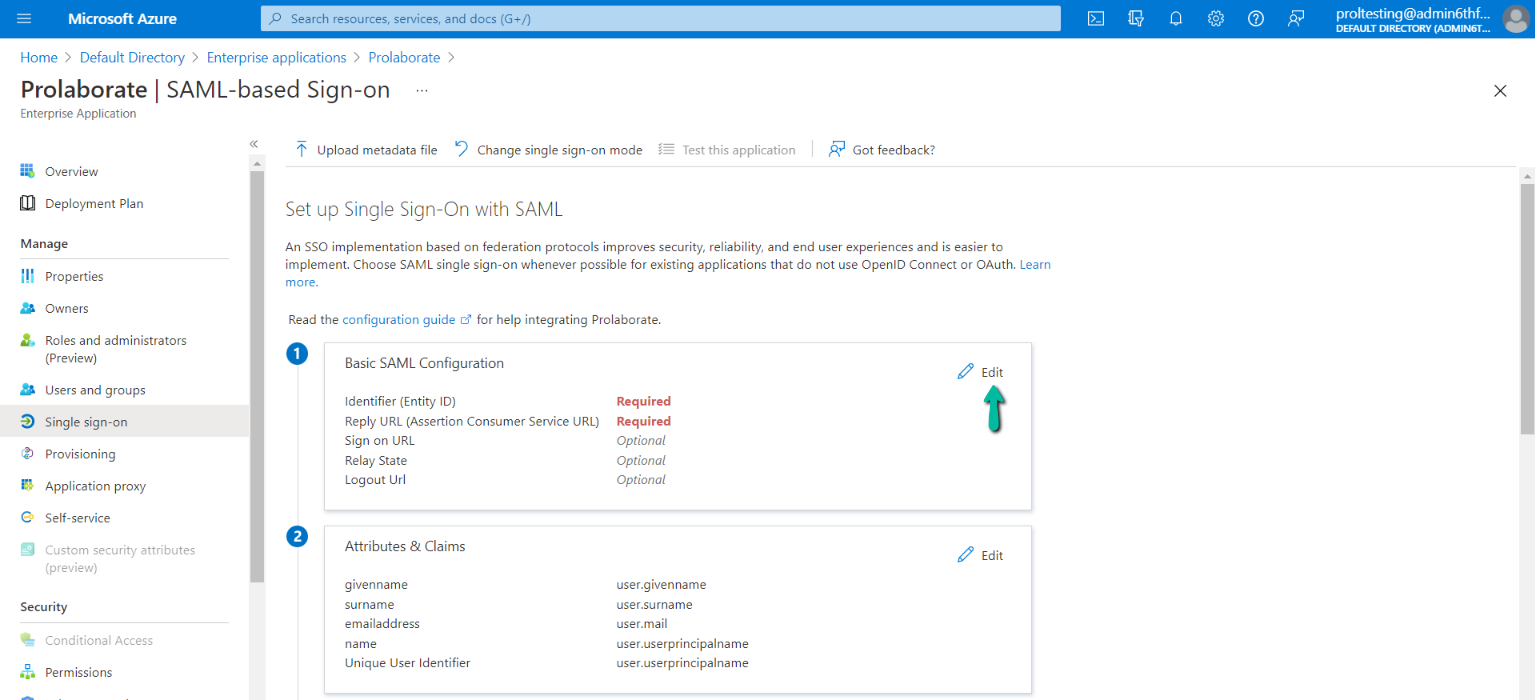
In the Basic SAML Configuration page enter the details in the respective fields as mentioned in the below table.
| Identifier (Entity ID) | In this field copy & paste the Name from the Prolaborate Service Provider configuration |
| Reply URL (Assertion Consumer Service URL) | In this field copy & paste the Assertion Consumer URL (ACU) from the Prolaborate Service Provider configuration |
| Logout URL | In this field copy & paste the Sign Out URL from the Prolaborate Service Provider configuration |
After entering the details click on Save.
You will then land on the below page on the successful configuration of SAML.
Configure Attributes Mapping in Prolaborate
To configure the Attribute Mapping in Prolaborate click on Edit Icon on the Attributes & Claims on the Set up Single Sign-On with SAML page.
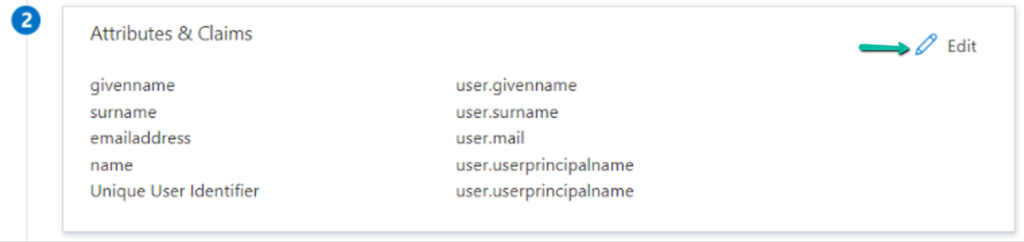
Copy the Attributes & Claims values from Azure AD and need to paste them into Prolaborate Attributes Mapping
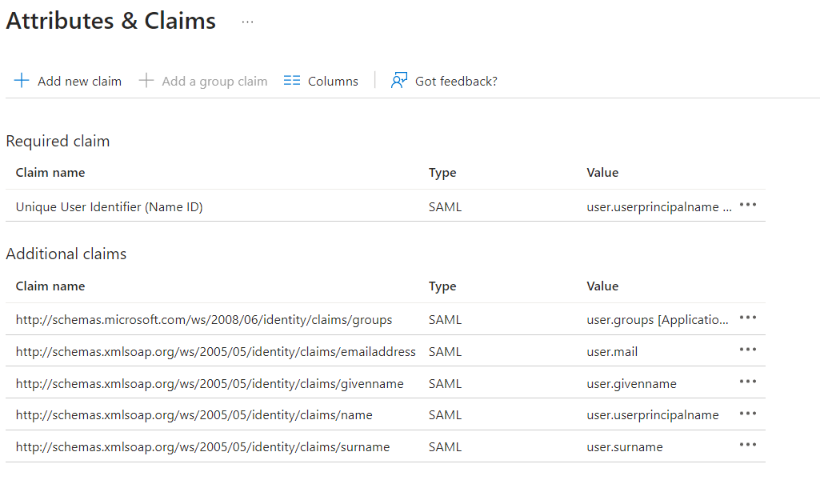
Attribute Mappings should be configured as below:
To enter the value, change the Attribute mapping from Default to Custom
| First Name | user.givenname (Copy the claim name from the Additional claims – Azure Page; part of the Attributes & Claim page and paste it into the Prolaborate Attribute mapping section of the Identity Provider setup.) |
| Last Name | user.surname (Copy the claim name from the Additional claims – Azure Page; part of the Attributes & Claim page and paste it into the Prolaborate Attribute mapping section of the Identity Provider setup.) |
| user.mail (Copy the claim name from the Additional claims – Azure Page; part of the Attributes & Claim page and paste it into the Prolaborate Attribute mapping section of the Identity Provider setup.) |
|
| Group | user.usergroup (Copy the claim name from the Additional claims – Azure Page; part of the Attributes & Claim page and paste it into the Prolaborate Attribute mapping section of the Identity Provider setup.) |
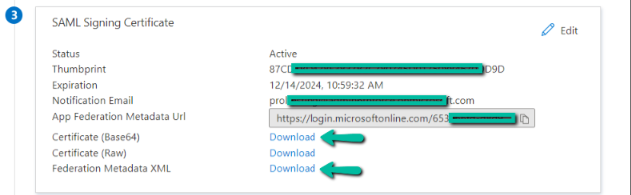
Download Signed Certificate for upload
- Download Certificate (Base64) file. This certificate will be used in the Identity Provider configuration in Prolaborate
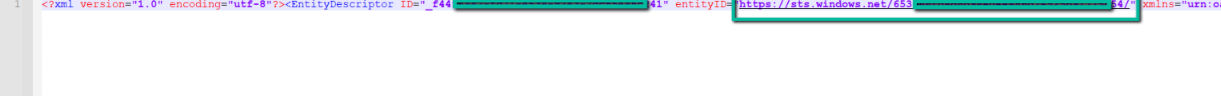
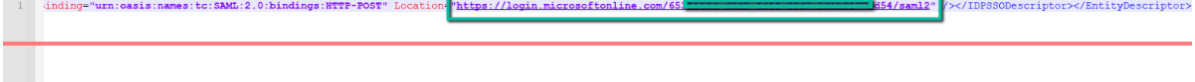
- Download Federation Metadata XML. You can avail Entity ID URL and Single Logout Service URL from this file, which will be used as Name and Sign out URL in Identity Provider configuration in Prolaborate
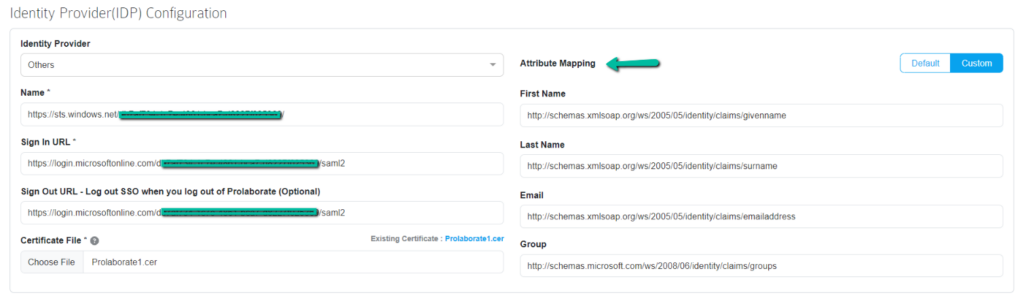
Configure Identity Provider in Prolaborate
Navigate back to Prolaborate, and click on Menu > SAML Single Sign On. Follow the steps to fill in the details in Identity Provider (IDP) Configuration.
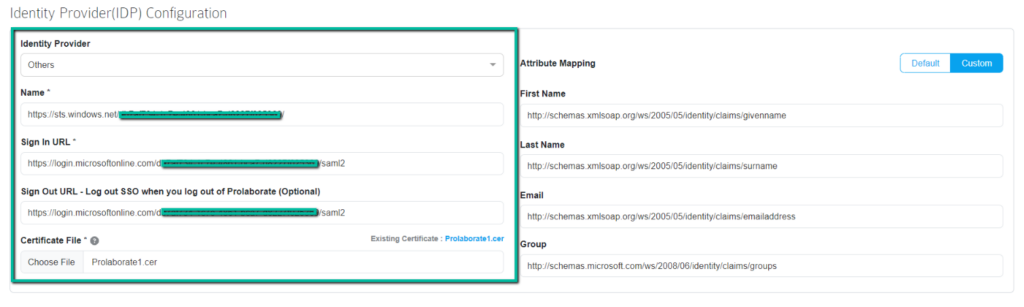
- Identity Provider – Select `Others` (learn more)
- Name – Fill the Name field using the Entity ID URL from the downloaded Federation Metadata XML file (Refer to section SAML Signing Certificate)
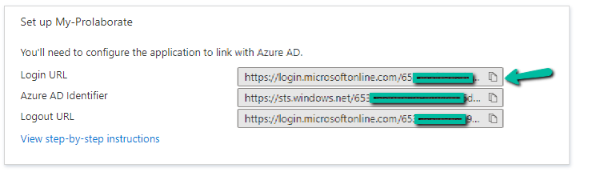
3. Sign In URL – Sign In URL will be the Login URL availed from the Set up My Prolaborate tab as shown below.
4. Sign Out URL – Fill the Sign Out URL field using Single Logout Service URL from the downloaded Federation Metadata XML file (Refer to section SAML Signing Certificate)
5. Certificate File – Choose the .cer file downloaded in the SAML Signing Certificate section.
Configure Default Access Control Profile in Prolaborate
Access Control Profiles let you define repository access rules and default user group membership for users added via SSO or Sign up.
Before configuring the Access Control Profile, it’s essential to understand User Group and Permission. Click here to learn how to set up access permissions for user groups.
Create Profile
To create an Access Control Profile, click on Menu > Access Control Profiles under portal settings.
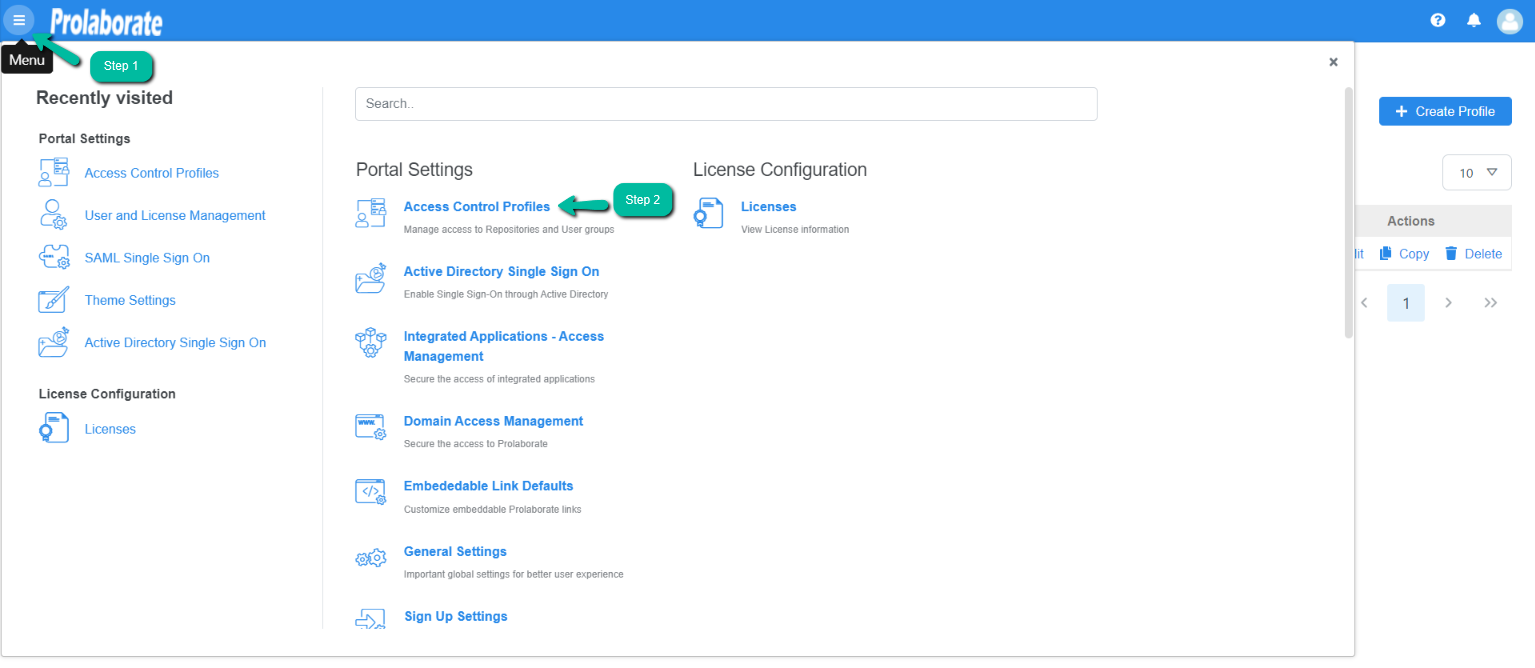
Access Control Profiles lists profiles which are created earlier. To create a new profile, click on Create Profile to create a profile
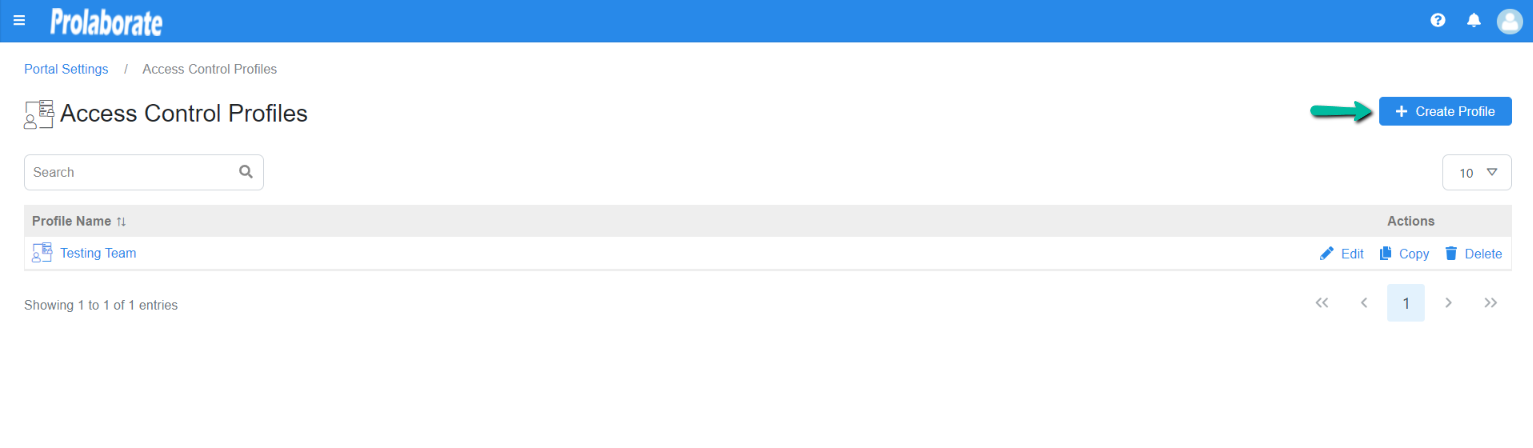
When you click on Create Profile you will land on the below page.
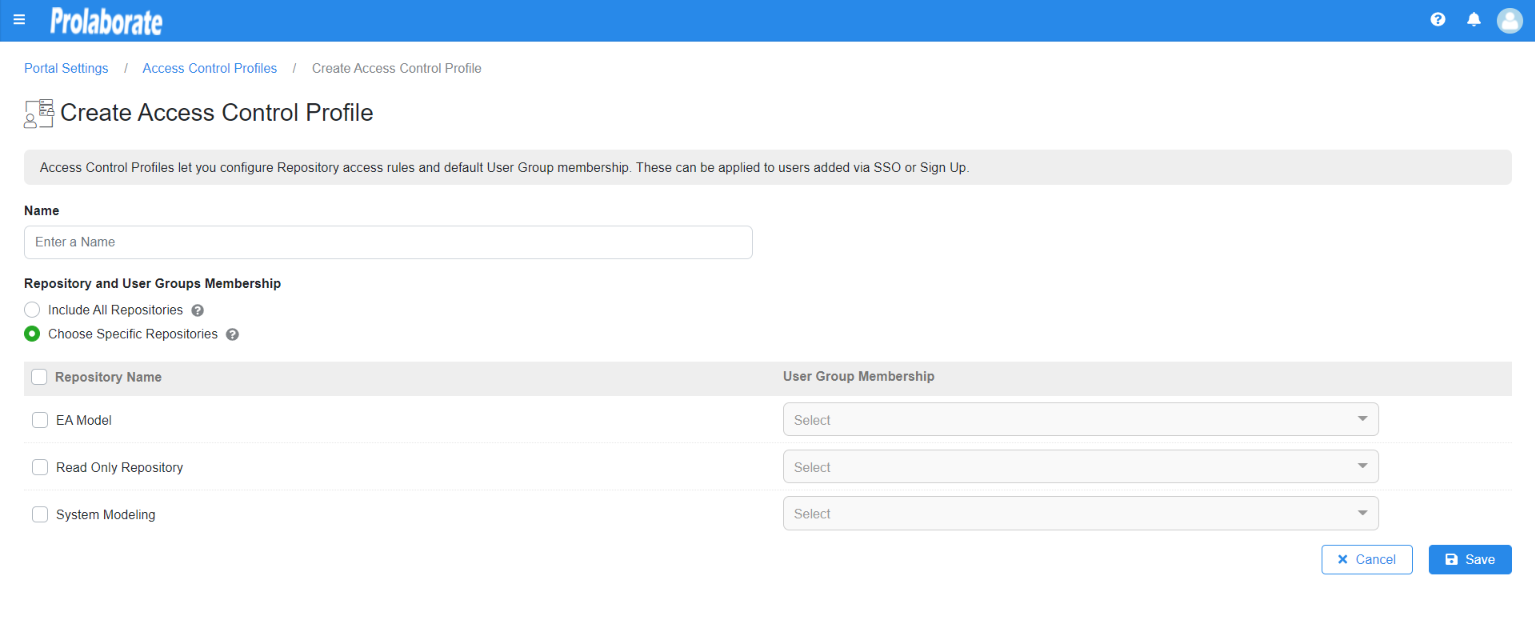
| Name | Give a suitable name for the profile |
| Include All Repositories | If you choose this, users who are logging in through SSO or Sign up will get access to all the repositories. |
| Choose Specific Repositories | This will let you choose the Repository and the corresponding User Group Membership and the user who is logging in through SSO or Sign will get access based on the user groups they are added to. |
Now click on Save.
Now, go back to the SAML Settings page.
Under the access control profile Toggle on ‘SAML group-based Restriction’
Select the newly created profile and click Save.
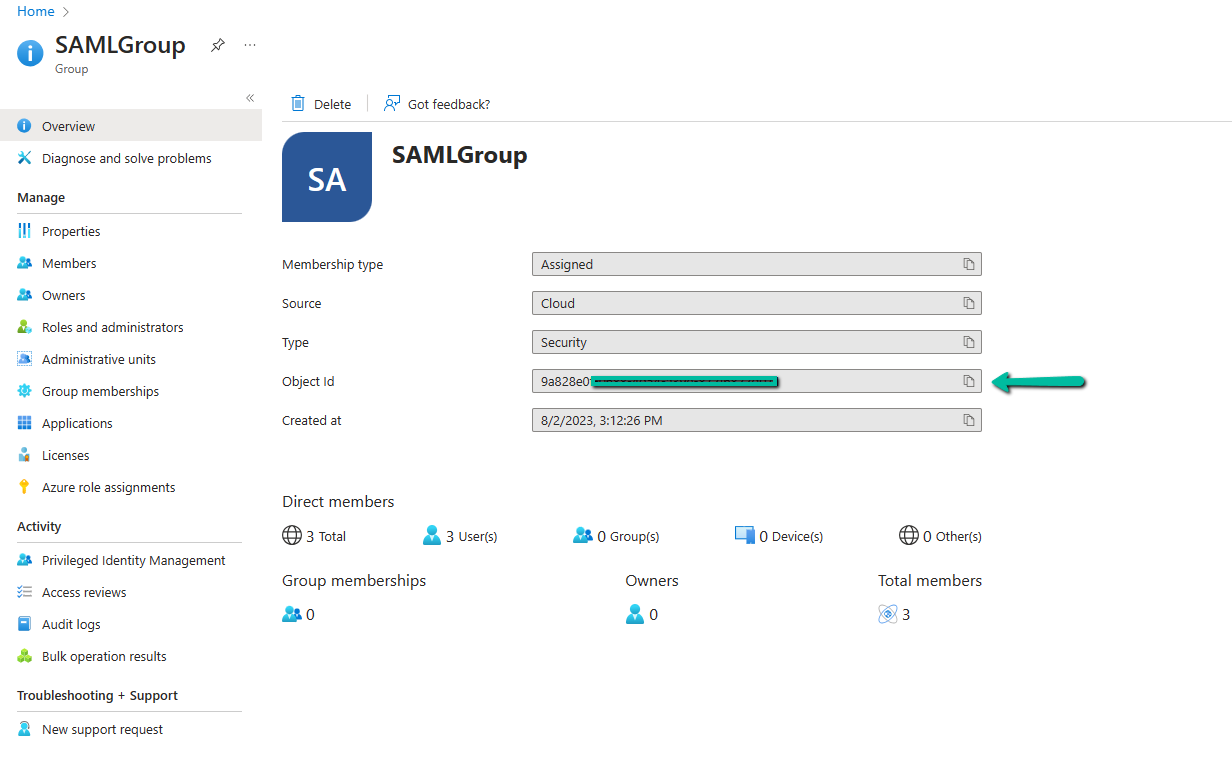
From Microsoft Azure AD copy the group Object ID and paste it under SAML group and click on save
Users are allowed to add multiple groups by using ‘Add’ button and follow the same procedure as explained in above sections.
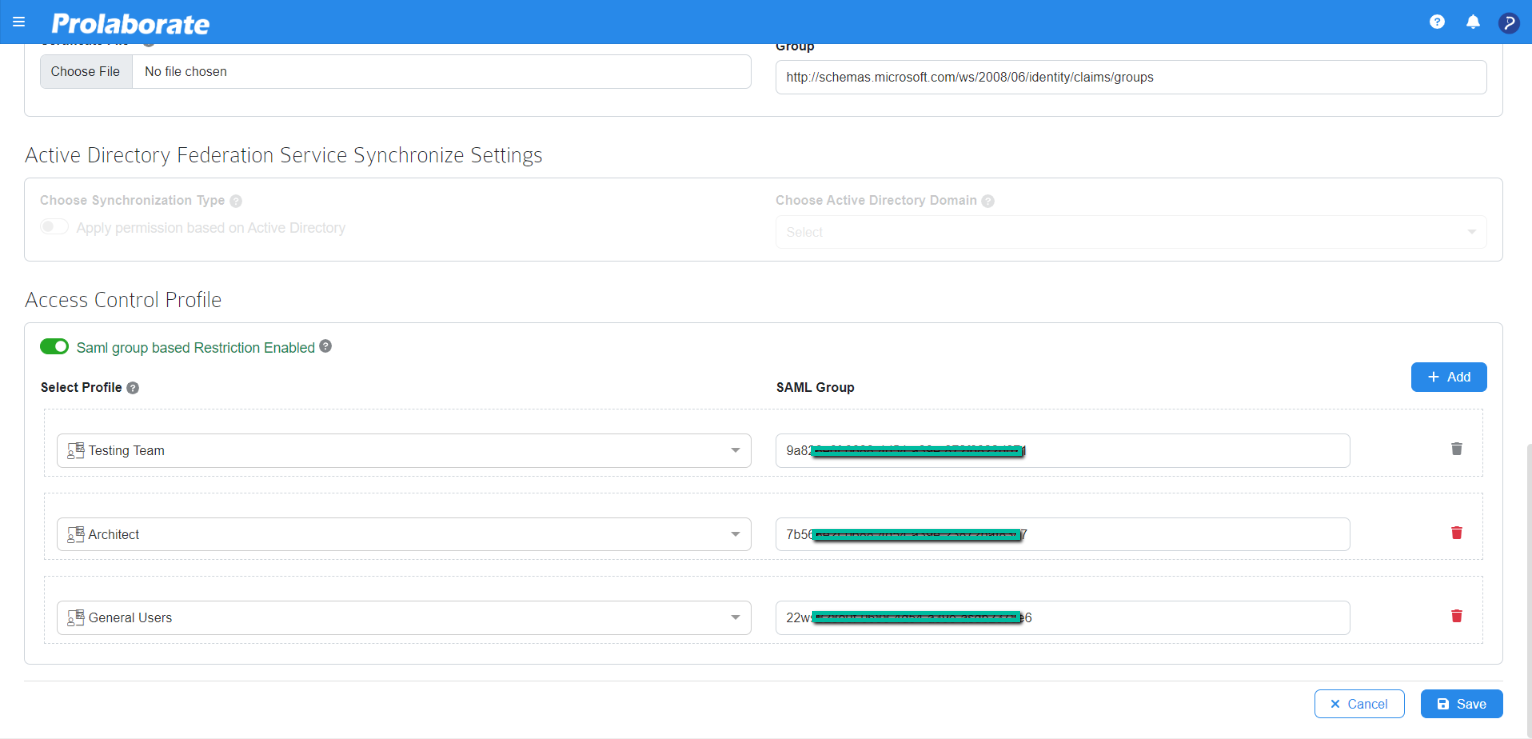
| Select Profile | User Group Access |
|---|---|
| Testing Team | Read/Write & collaborate |
| Architect | Read & collaborate |
| General Users | Read-Only |
By Enabling `SAML group-based restriction `, Prolaborate can restrict the user groups to distinguish the access that they want to acquire.
Log in with Azure AD Credentials
Once the configuration is done, your users will start to see a new button on the login page called Login with SSO.
When users click on Login with SSO, they will be redirected to an URL as per configuration.
Now enter the Azure AD credentials to login to Prolaborate.
If you’re experiencing challenges signing in using SSO, go at SAML Assertion Validation to debug the SAML configurations.
Login screen can be customized to show only LOG IN WITH SSO button whenever SAML Single Sign On is configured. Click here to know more.
Logging out from Prolaborate
When a user logs out from Prolaborate, the user will be logged out from all applications signed in using their SSO credentials.